In our rapidly advancing digital age, cybersecurity has become one of the most critical aspects of modern life. As technology continues to evolve, so do the threats that come with it. From AI-driven cyberattacks to data breaches targeting businesses and individuals alike, the digital landscape in 2025 is more connected — and more vulnerable — than ever before.
Thank you for reading this post, don't forget to subscribe!With millions of devices linked through the Internet of Things (IoT), cloud computing, and 5G networks, safeguarding personal and organizational data has never been more essential. This article explores the state of cybersecurity in 2025, the emerging threats, and practical ways to protect your data in this increasingly digital world.
1. The Current Cybersecurity Landscape in 2025
The year 2025 represents a turning point in global cybersecurity. As digital transformation accelerates, cybercriminals have become more sophisticated, targeting not only large corporations but also small businesses, governments, and individuals.
a. The Growth of Digital Interconnectivity
With smart homes, wearable tech, and AI-driven systems everywhere, every connected device can serve as a potential entry point for hackers.
According to recent studies, over 75 billion devices are now connected globally — creating a vast web of potential vulnerabilities.
b. The Rise of AI-Enhanced Cyber Threats
Hackers now use artificial intelligence (AI) and machine learning (ML) to automate and enhance their attacks.
These intelligent systems can identify weak points, mimic human behavior, and even bypass traditional security systems — making manual defenses obsolete.
c. Cloud Computing Risks
The massive adoption of cloud storage and remote work tools means sensitive data is constantly being transferred and stored online.
Without strong encryption or access controls, this data becomes an easy target for cybercriminals.
2. Emerging Cyber Threats to Watch Out for in 2025
As technology evolves, so do the methods cybercriminals use to exploit it. Below are the most pressing cybersecurity threats in 2025:
a. AI-Powered Attacks
Hackers now deploy AI-driven malware capable of learning and adapting in real time. These systems can avoid detection, change their code signatures, and strike at the most vulnerable moments.
AI is also used to create deepfakes — hyper-realistic fake videos and voices — to manipulate users and spread misinformation.
b. Ransomware Evolution
Ransomware remains one of the biggest threats in 2025. Cybercriminals don’t just encrypt files anymore; they steal data and threaten to leak it if ransoms aren’t paid.
This new form, known as “double extortion ransomware,” is more aggressive and costly, often targeting hospitals, government systems, and major corporations.
c. Internet of Things (IoT) Vulnerabilities
Smart devices like cameras, thermostats, and even cars are often manufactured with weak security protocols.
Hackers can exploit these devices to gain entry into larger networks, spy on users, or cause disruptions in connected systems.
d. Cloud Security Breaches
With most companies shifting data to the cloud, misconfigured servers and poor access management have become leading causes of data breaches.
Cybercriminals exploit these weaknesses to steal massive amounts of sensitive data, from personal information to financial records.
e. Phishing 2.0
Phishing emails are no longer filled with obvious spelling mistakes or fake logos.
In 2025, phishing campaigns use AI to personalize attacks. These messages appear so authentic that even the most cautious users can fall victim.
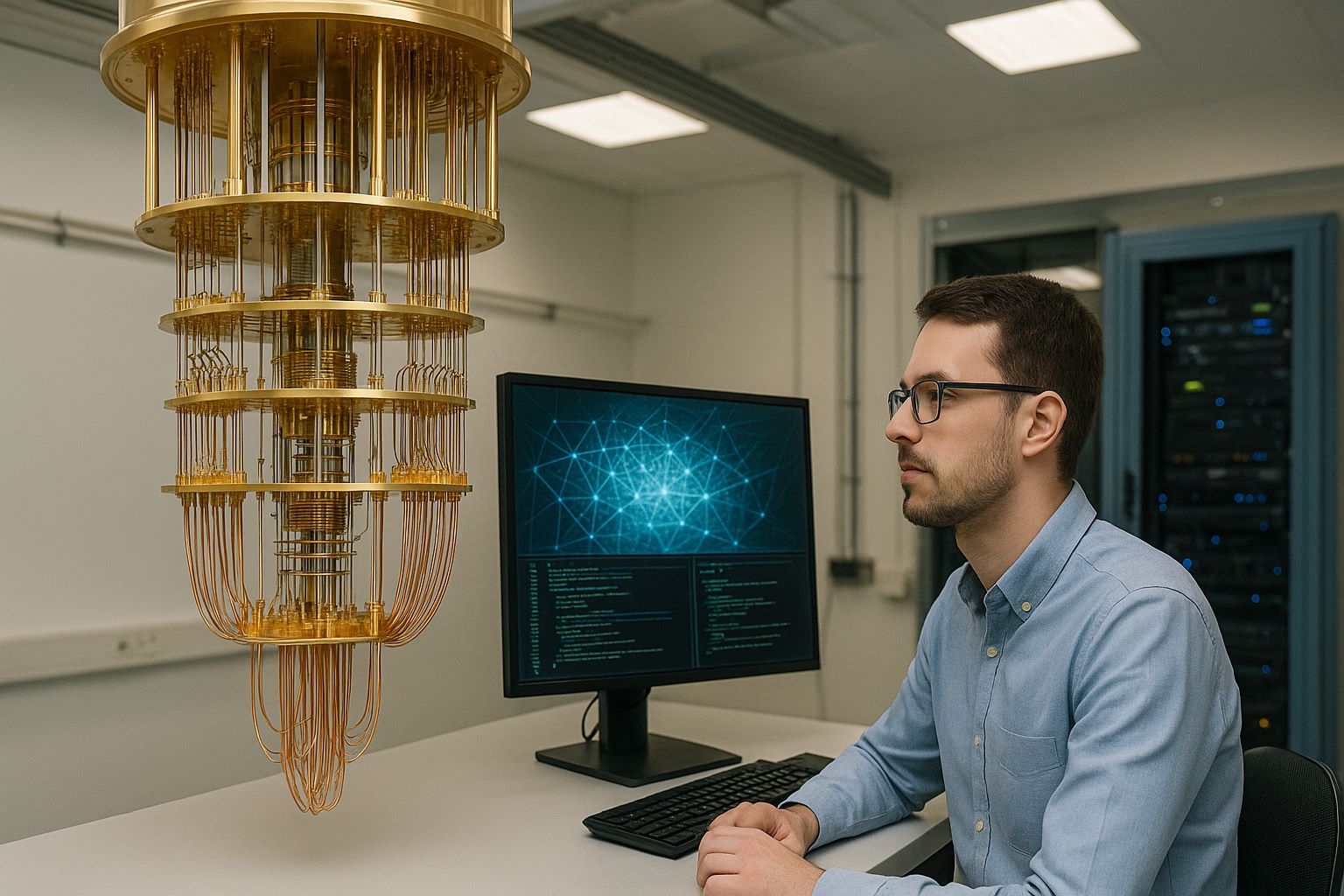
f. Quantum Computing Threats
Quantum computing has the potential to break current encryption methods, posing a serious long-term risk to global cybersecurity.
While still in early stages, experts warn that data encrypted today could be vulnerable to decryption by quantum systems in the near future.
3. Industries Most at Risk
Every industry faces cybersecurity challenges, but some are more vulnerable than others.
a. Healthcare
Hospitals and clinics store highly sensitive data — from patient records to genetic information.
Cyberattacks can disrupt services or expose confidential data, making cybersecurity in healthcare a matter of life and death.
b. Finance
Banks and financial institutions are top targets for ransomware and data theft.
Even a brief breach can lead to huge monetary losses and reputational damage.
c. Government and Defense
Nation-state cyberattacks have increased dramatically. In 2025, cyber warfare is a growing threat as countries target each other’s infrastructure, data, and communication systems.
d. Education
Universities and schools hold personal data and research information, making them prime targets for hackers seeking easy entry points and valuable data.
4. The Role of Artificial Intelligence in Cybersecurity
While AI can empower cybercriminals, it’s also a powerful ally for cybersecurity professionals.
a. Predictive Threat Detection
AI systems can analyze billions of data points to predict and detect attacks before they happen.
By learning from past patterns, AI can flag suspicious behavior, isolate threats, and prevent breaches in real time.
b. Automated Security Response
AI-powered tools automate responses to cyber incidents, reducing the time between detection and action.
This minimizes damage and keeps systems operational during attacks.
c. Behavioral Analysis
Advanced AI tools monitor user activity to identify anomalies — such as unusual login locations or access attempts — helping prevent unauthorized actions.
d. Adaptive Defense Systems
Unlike traditional firewalls, AI-driven defenses evolve continuously, adapting to new attack methods as they emerge.
5. How to Protect Your Data in 2025: Best Practices
Now that we understand the threats, let’s focus on practical cybersecurity measures that individuals and businesses can adopt in 2025.
a. Strengthen Passwords and Authentication
- Use strong, unique passwords for every account.
- Implement multi-factor authentication (MFA) wherever possible.
- Consider using password managers to store credentials securely.
b. Regular Software Updates
Outdated software is one of the easiest ways hackers gain access.
Always install system and app updates promptly — they often include critical security patches.
c. Secure Your Wi-Fi and Devices
- Change default passwords on routers and smart devices.
- Use strong encryption methods like WPA3 for Wi-Fi networks.
- Avoid using public Wi-Fi for sensitive transactions unless using a VPN (Virtual Private Network).
d. Backup Your Data
Regularly back up important files to both cloud and offline storage.
In case of ransomware attacks or hardware failures, you’ll be able to restore your information quickly.
e. Educate Yourself and Your Team
Cybersecurity awareness is your first line of defense.
Train employees to recognize phishing attempts, use secure networks, and follow company security protocols.
Regular cyber hygiene training can prevent most human-error-based breaches.
f. Use Encryption Everywhere
Ensure all sensitive data — both stored and transmitted — is encrypted.
End-to-end encryption makes it nearly impossible for hackers to read intercepted data.
g. Deploy AI and Zero Trust Security
Adopt a Zero Trust framework — never assume anyone or any device is automatically trustworthy.
Combine this with AI-based monitoring tools that verify users and continuously assess risk.
h. Monitor Your Accounts and Networks
Use real-time monitoring software to track network activity and flag unusual behavior.
Individuals can also set up alerts for unauthorized logins or unusual spending on financial accounts.
6. Government Regulations and the Future of Cyber Laws
Governments around the world are introducing stricter regulations to protect user data.
By 2025, laws such as the EU’s GDPR, California Consumer Privacy Act (CCPA), and new AI Ethics Regulations are shaping how companies collect, use, and store data.
These frameworks demand transparency, accountability, and user consent, ensuring that organizations prioritize data protection at every stage.
7. The Future of Cybersecurity Beyond 2025
The cybersecurity battle is far from over. Experts predict several major trends that will define the future:
- Quantum-Resistant Encryption: New encryption methods will emerge to combat quantum computing threats.
- AI-Powered Cyber Defense: AI will handle nearly 80% of security operations autonomously.
- Global Cybersecurity Collaboration: Nations and tech companies will cooperate to combat global threats.
- Digital Identity Protection: Advanced biometric and blockchain-based ID systems will replace traditional passwords.
In short, cybersecurity will become more intelligent, automated, and proactive than ever.
8. Conclusion
As we navigate deeper into the digital era of 2025, one truth stands out: cybersecurity is no longer optional — it’s essential.
Every click, connection, and cloud service introduces a potential risk, making awareness and proactive defense the best weapons against cyber threats.
Protecting your data is not just about using technology — it’s about adopting a security mindset. Whether you’re an individual, entrepreneur, or organization, taking preventive measures today ensures safety tomorrow.
The future will be connected, but with the right cybersecurity practices, it can also be secure.